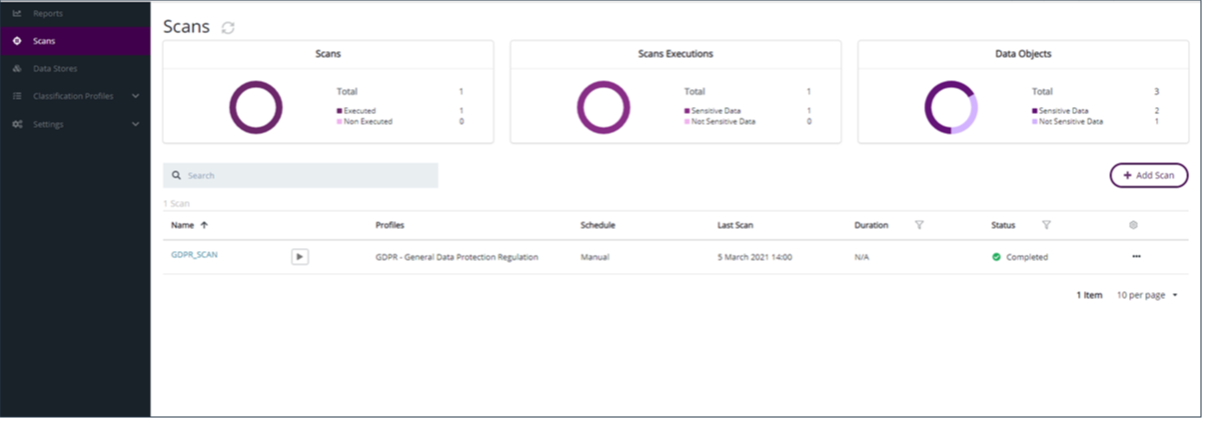
Scans
You must configure the scan for the data discovery. Select the datastore that contains the sensitive data for data discovery and the profile/s used to classify the sensitive information found. You can also set the scheduling for the scan execution.
DDC scan performs GuardPoint and policy validation in two phases to avoid chances of misconfiguration:
Enabling Remediation: The first validation is performed while enabling remediation for a DDC scan. DDC sends a request to check whether the CTE client and the GuardPoint corresponding to the specified datastore hostname and the scan target path exist.
Scan Execution: The second detailed validation is performed while scan execution. DDC sends a request to CTE to validate the following information:
CTE client
CTE GuardPoint status, classification status, and rekey status for LDT policy
Classification profile used in the resource set against the profile used in the scan
Note
If you are unclear about enabling remediation, you can create a scan without remediation. You can then view the report and, if you feel the need for remediation, modify the scan to enable and configure remediation. The remediation will be triggered with the next run.
Adding Scans
In CipherTrust Data Discovery and Classification, click Scans.
Click Add Scan.
Type in the name and description and click Next.
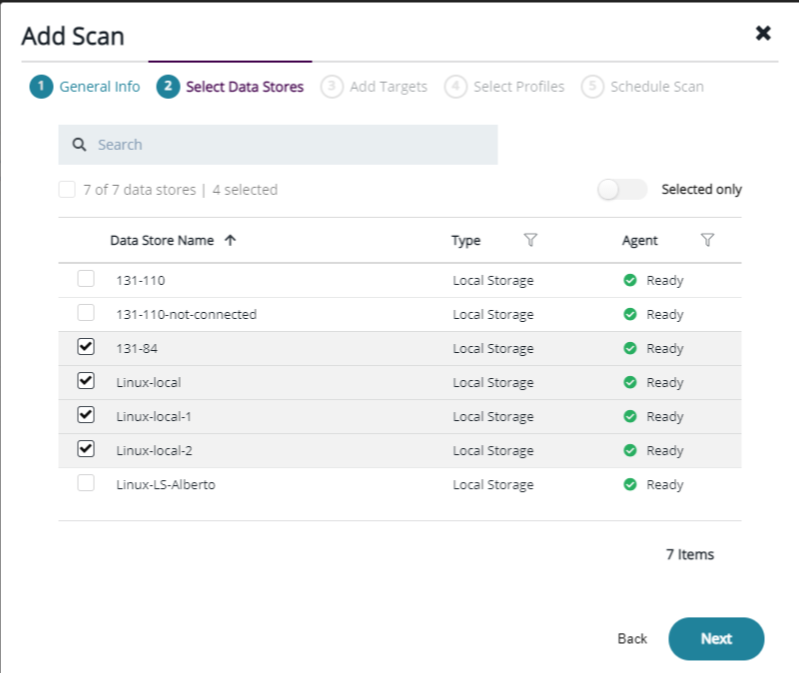
Select all of the data stores with sensitive information on them to scan.
Note
When you create reports, you select which scans to include in the report. Therefore, only choose the Data Stores that you want to be included in the same report. Note that scans can be added to multiple, independent, reports.
Type the path for the Data Discovery target in the Add Target field, and click Apply to assign the target to the Data Store.
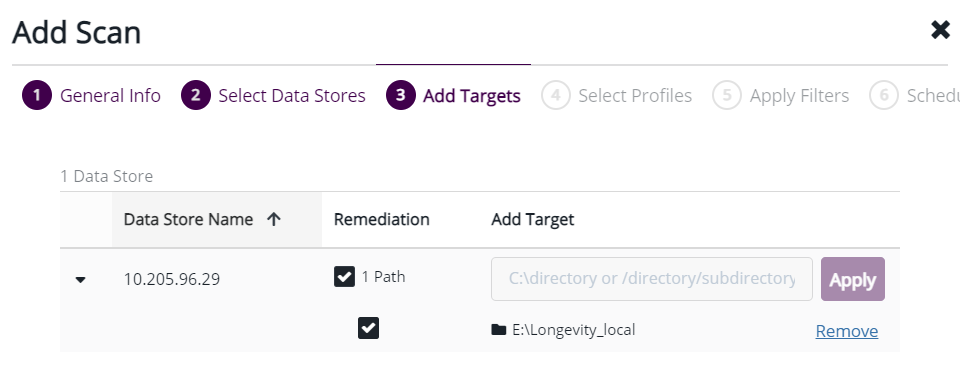
Once you add the target, if you click on the down arrow, the target path and a checkbox appears (to enable remediation).
Note
This checkbox (to enable remediation) only activates if:
Data store type is a Local/Network file system
Client has both a DDC and CTE agent installed
DDC Data Store IP Address/Hostname matches CTE name
DDC scan path matches the active GuardPoint path
Click checkbox to enable remediation.
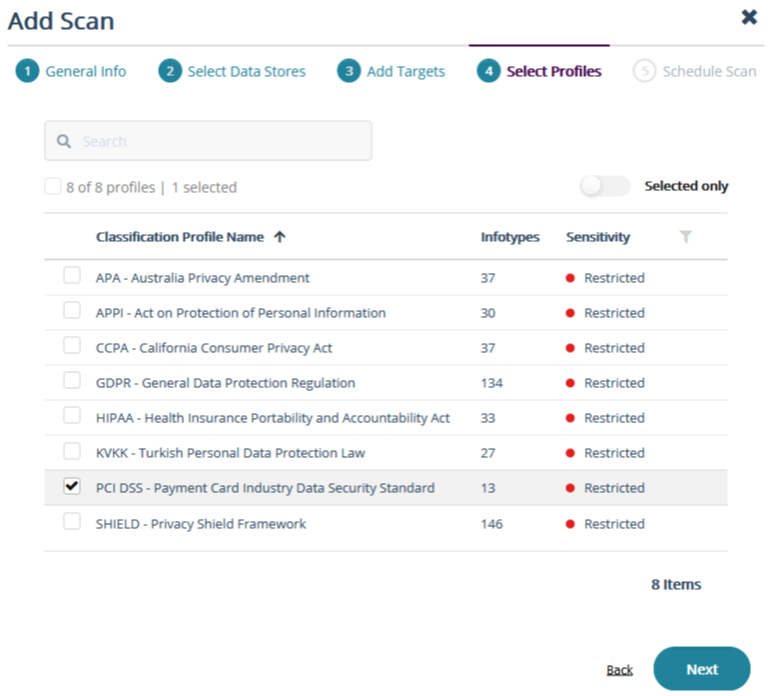
Select the Classification Profile to apply to the scan and click Next.
Note
The Classification profile must match the Classification Profile used in your CTE policy and Resource Set.
For the frequency, select Manual or Scheduled the scan for a later date.
Click Run Now to execute the scan immediately after saving and closing the wizard.
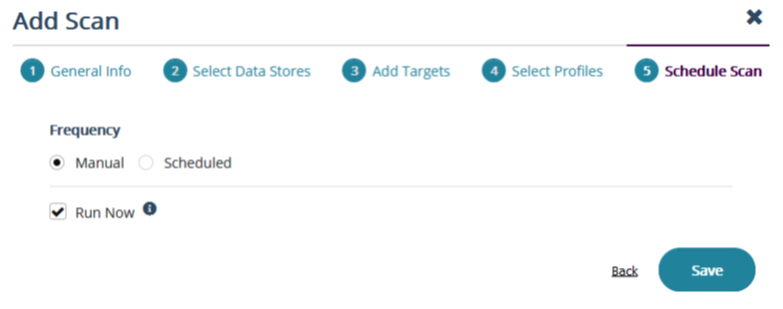
Click Save to close the wizard. The scan starts the discovery process automatically. When the scan is finished, the status changes to Completed.
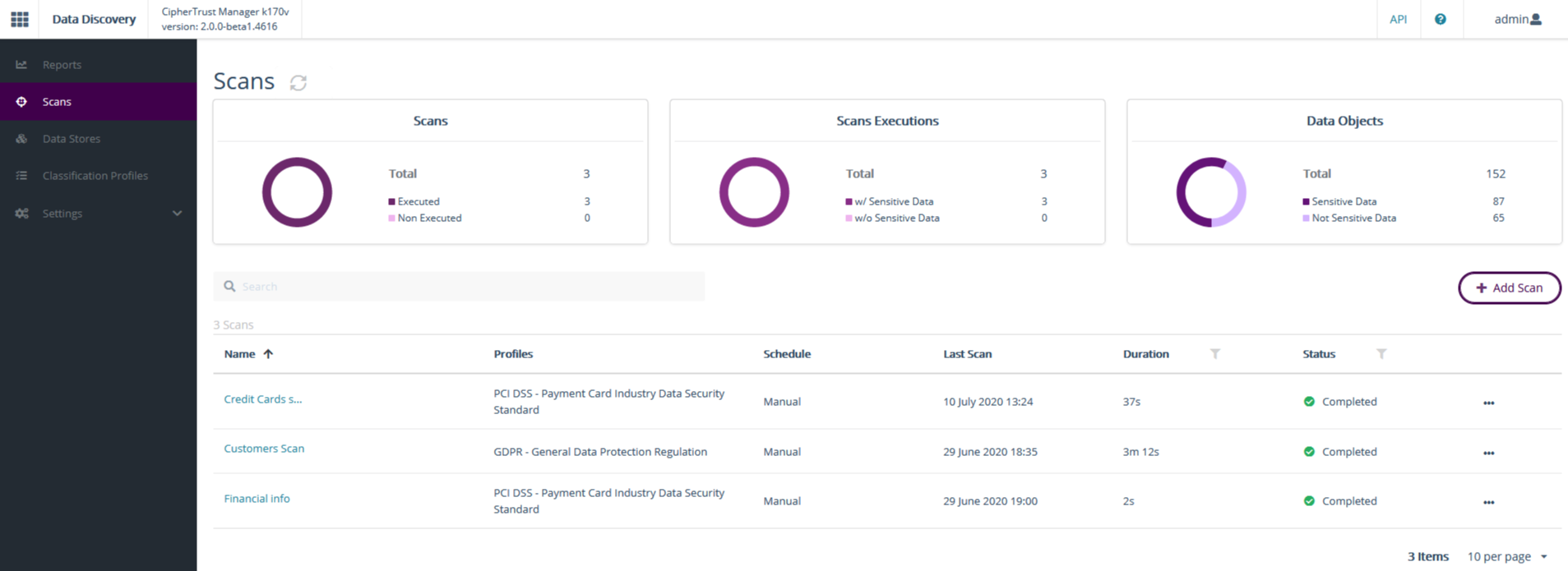
Once the scan is finished, you can generate a report to see all of the information discovered and classified by the tool.
Alternatively, to run the scan after the initial configuration, click the arrow key next to the scan name.
Scanning for Remediation
The DDC scan classifies files and sends a notification to CTE to perform remediation on sensitive files. CTE performs the required remediation on all classified files according to policy and updates the remediation information like encryption key, encryption time for each file. The result of classification and remediation can be visualized on the DDC report.
Warning
The Scan execution or reclassification is required to fetch and update the remediation status in reports.
Following is the process for scanning and remediating files:
CipherTrust Data Discovery and Classification runs the initial scan and scans all of the files.
CipherTrust Data Discovery and Classification sends a message to CipherTrust Transparent Encryption as to which files require remediation.
CipherTrust Transparent Encryption remediates the data.
Note
The duration of the remediation depends on how many files are being remediated and the size of the files.
To see the effects of remediation in the reports, CipherTrust Data Discovery and Classification must perform a second scan. This scan is performed on the remediated files.
After this second scan completes, it reads information from TDP about the status of each file that needed remediation. That information is captured in the scan results which are then stored in TDP.
When a new report is generated and the DDC admin specifies the second scan, the report will then contain detailed information about the remediated files.
Remediation Status
Scan with Remediation Enabled and Reclassify options wait for remediation to be completed.
After the DDC scan is completed, users can generate reports without running the Reclassify option.
Remediation Status feature is not available for the GuardPoints applied on the Linux Local Data Store with LDT policy.
Remediation Status feature is supported with CTE release 7.4 and higher.
Reclassification
The DDC scan has a new action, Reclassify, to trigger remediation related operations. This action is available only for completed scans. This action serves two purposes:
Update classification information for remediation on already scanned data.
Fetch updated remediation information from CTE for DDC reports.
The Reclassify option requests CTE to validate GuardPoint and policy configuration. The action works for existing scanned data. A complete scan should be executed to sync the file system changes like new file creation, rename, and move operations.
SMB/CIFS Scan
Refer to Managing Scans for details.

