Reports
The CIP solution provides reports to visaulaize data scan, classification, and remediation result in tabular and graphical view. CIP supports the following reports:
Aggregated Reports: Display high-level aggregated information for selected scan(s) to analyze the status of associated data stores. Refer to Reports of Data Discovery and Classification for details.
Trend Reports: Display how the scan and remediation information evolves over time. Refer to Reports of Data Discovery and Classification for details.
Generating Reports
CIP reports can be created and generated on the DDC report page. Refer to Creating Reports for details on DDC reports.
Analyzing Reports
DDC reports provide useful information about the remediation of data objects. This information can be analyzed to identify remediation status, view remediation details, and review remediation strategy.
Aggregated Reports
The Data Objects tab provides information about data objects and their remediation. The icons on the left of the object names indicate the remediation status of the sensitive object found. The following lists the possible remediation statuses:
| Icon | Description |
|---|---|
 | (Not Supported) The data object is found in an unsupported datastore/target, so it could not be remediated. Currently, remediation is only supported on local storage data store types. |
 | (Disabled, Outside GuardPoint, No CTE Agent) The data object cannot be remediated due to one of these reasons: Remediation is not enabled on that particular target of the scan where the object was found. Remediation is enabled, but the object is outside the GuardPoint so CTE cannot remediate it. No CTE Agent is configured on the scanned data store. |
 | (Unencrypted – Inside GuardPoint) This usually happens when a sensitive object is detected for the first time by a scan. In this case, the scan will remediate it (by encrypting it), however, it will report it as “unencrypted” to indicate the status of the object at the time it was found. Running a scan the next time with this object in it will report it as “encrypted”. |
 | (Encrypted – Inside GuardPoint) Indicates a correctly remediated data object with Encryption and Access Control. |
 | (Inside ACL Only) Indicates a remediated data object with Access Control Only. No encryption is applied. |
Remediation Information
An aggregated report also provides more details about the remediation of each data object. This information can be viewed by expanding the report row for any data object.
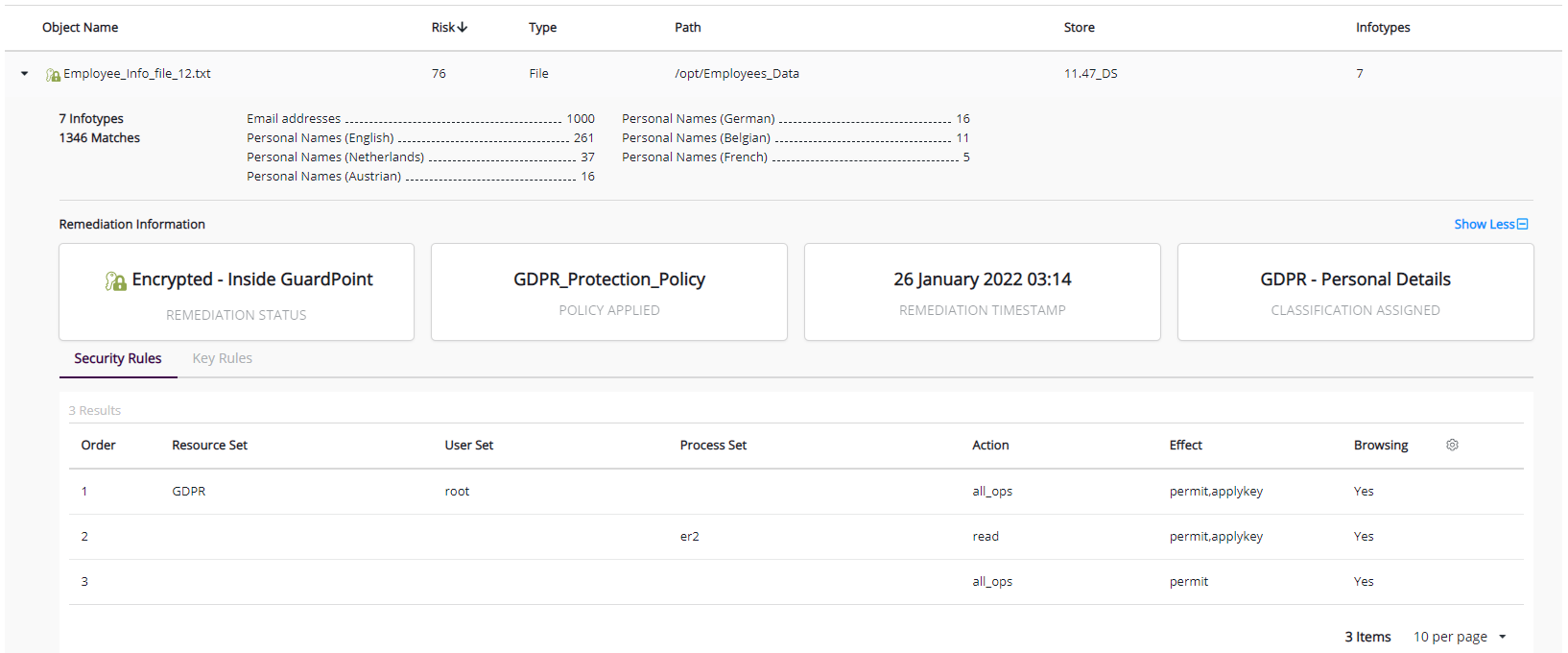
The Remediation Information section features the following cards:
REMEDIATION STATUS
POLICY APPLIED
REMEDIATION TIMESTAMP
CLASSIFICATION ASSIGNED
The Remediation Information section also provides information related to Security Rule/s and Key Rule/s that are part of the CTE policy applied on the target path while creating GuardPoints.
REMEDIATION STATUS
The REMEDIATION STATUS card shows the remediation applied to the data object. The possible remediation statuses are:
Not Supported: Appears for data objects that belong to a data store that does not support remediation. Currently only, LOCAL STORAGE data stores support remediation.
The statuses for data objects that belong to a local storage type data store are:
No CTE Agent: Appears for data objects that belong to a data store that does not have a CTE agent installed.
Outside GuardPoint: Appears for data objects that have a CTE agent installed, but the path that contains this data object is not behind a GuardPoint.
The statuses for targets that have a CTE agent running in the DataStore, and where data objects are behind a GuardPoint are:
Disabled: Appears for data objects that belong to a path that was remediated unintentionally.
Unencrypted - Inside GuardPoint: Appears for data objects that belong to a path that was remediated, but the data object was not encrypted at the moment the scan was run (this could be due to several reasons).
Note
On the first scan, the found sensitive data objects that are being remediated are shown as “Unencrypted – Inside GuardPoint”, as the report reflects the status of the object at the time of the scan run. Running a "Reclassify" operation on a completed scan or executing a scan the second time on the same data objects will report that they were remediated and encrypted (“Encrypted – Inside GuardPoint”). If data objects are not changed on the target path, the Reclassify option should be used, as this only fetches remediation information and takes less time.
Encrypted - Inside GuardPoint: Appears for data objects that belong to a path that was remediated, and the data objects are now encrypted.
Inside ACL Only: Appears when an Access Control List (ACL) Only policy is defined in the CTE configuration. Data objects are not encrypted, only the access control is managed according to CTE policies.
POLICY APPLIED
The POLICY APPLIED card displays the name of the CTE policy used to protect the GuardPoint.
REMEDIATION TIMESTAMP
The REMEDIATION TIMESTAMP card shows the timestamp when the remediation was applied by CTE. For an encryption-based policy, this value refers to the time when the file encryption was completed. For access control only policies, this value refers to the time when CTE enforced the access rules according to the policy.
CLASSIFICATION ASSIGNED
The CLASSIFICATION ASSIGNED card shows the classification profile applicable to the data object identified during the scan.
Trend Reports
A trend report shows how the scan information evolves. Trend reports have three graphs that show information related to remediation progress over time.
Data Objects: Shows the count of data objects scanned, identified as sensitive, and remediated. The left axis displays the count of data objects. To view details about the displayed parameters at any specific time, move the mouse over the graph area.
Note
The data object for local storage and network storage type datastores is a file.
Average Risk: Shows the effect of remediation on risk. The risk scope reduces with an increase in the count of remediated objects.
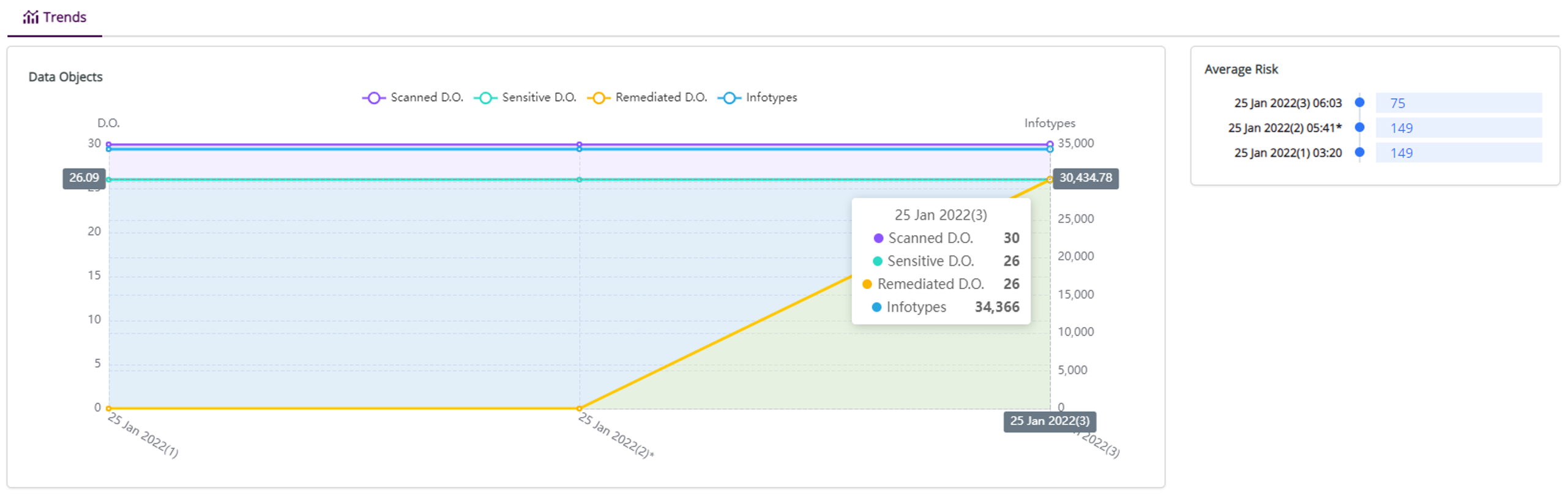
Remediation: Shows the count of sensitive, remediable, and remediated data objects.
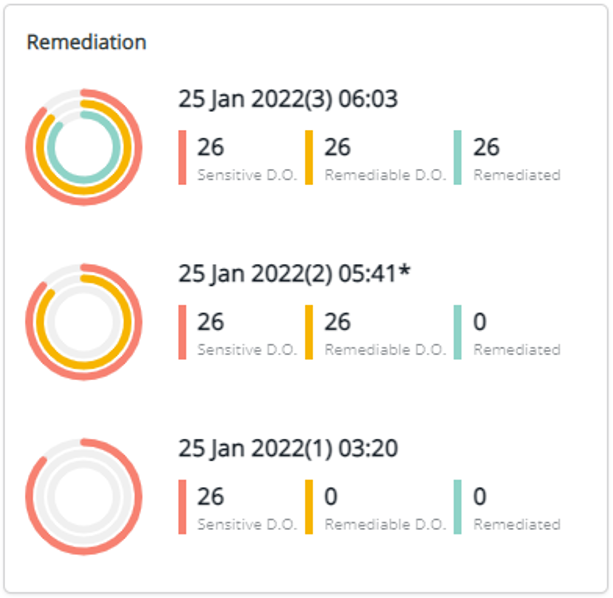
Sensitive D.O.: The count of sensitive data objects identified during the scan.
Remediable D.O.: The count of data objects that can be remediated.
Remediated D.O.: The count of data objects that are remediated.
NAS Reports (NFS/SMB/CIFS)
Refer to Reports of Data Discovery and Classification for details.
Note
A DDC scan agent can scan the LDT metadata folder within guard path. Therefore, the count of total data objects in the DDC report increases by the number of files added in the LDT metadata folder (it is the number of nodes in a client group plus 2) after the LDT policy is active.

