Identity Provider Settings
Identity Provider (IDP) Settings enables integration between the Thales Authenticator Lifecycle Manager and enterprise identity systems allowing seamless user authentication and access management. This integration involves configuring endpoints and parameters required for secure communication with IDPs. After the integration is complete, administrators can search for IDP users and enroll or revoke FIDO devices for those users.
The following identity providers are supported:
-
Microsoft Entra ID (Azure AD)
-
SafeNet Trusted Access (STA)
-
PingOne
-
Okta
Identity Provider Settings Table
The Identity Provider Settings table displays all configured identity providers along with their current status and available actions.
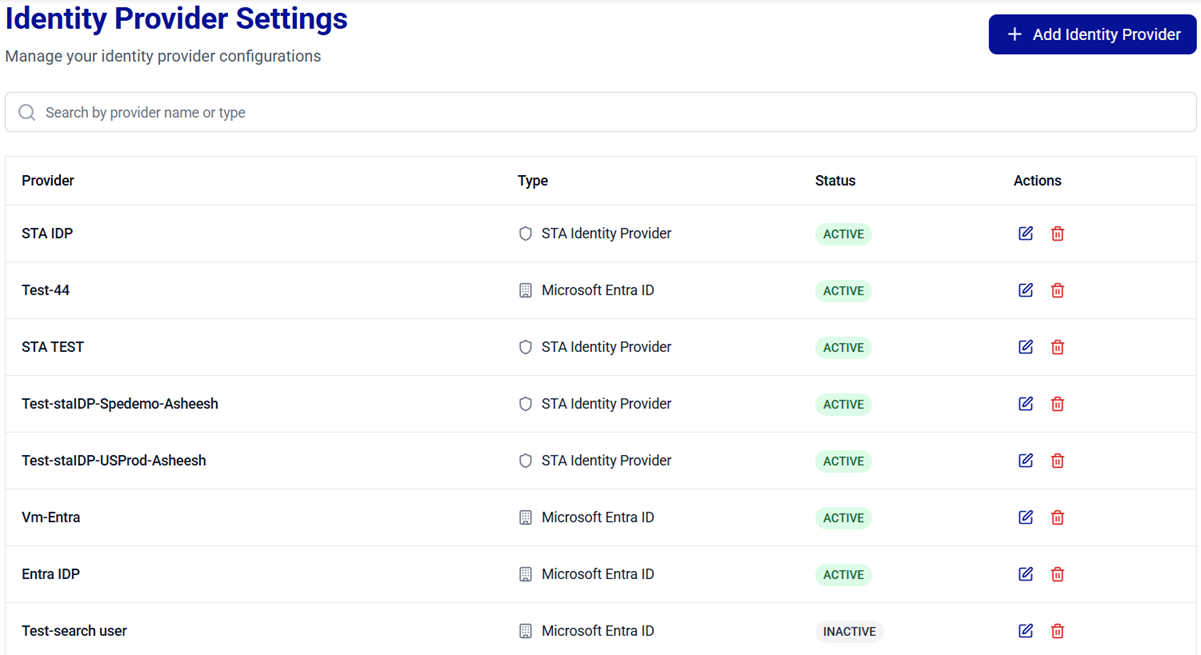
The following table explains each column given in the Identity Provider Settings table.
| Column | Description |
|---|---|
| Provider | Name of the identity provider. |
| Type | Identity provider type. |
| Status | Indicates the following status of identity provider: - ACTIVE: Configured, connection successfully tested, and available for communication with IDPs for user search and enrollment related operations. - INACTIVE: Configured but connection not yet tested. |
| Actions | Available actions: - Edit an identity provider  - Delete an identity provider  - Set a default identity provider  . . |
Manage IDP Integrations
Administrators can perform the following operations to manage IDP integrations:
- Search Identity Providers
- Add an Identity Provider
- Edit an Identity Provider
- Delete an Identity Provider
- Set a Default Identity Provider
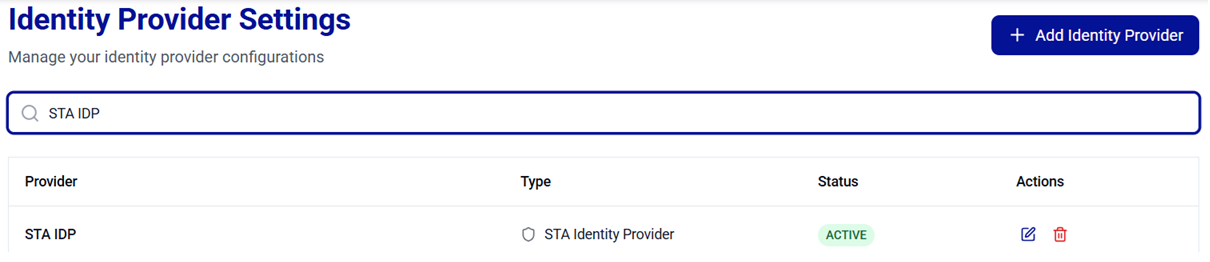
Search Identity Providers
The Search feature allows administrators to quickly locate identity providers. Use the search bar to filter identity providers and view their details based on either the identity provider name or type.
Add an Identity Provider
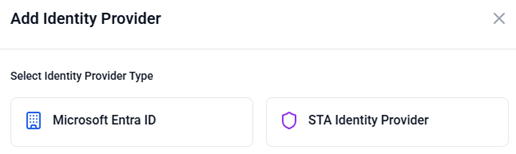
The Add Identity Provider button, located in the top-right corner of the Identity Provider Settings window, allows you to select and configure an identity provider.
Caution
- IDP credentials are case sensitive (for example, Client Secret for Entra ID, API Key for STA).
- Ensure that Console access is restricted to authorized administrators and credentials are stored securely in accordance with your organization’s security policies.
-
On the Identity Provider Settings window, click Add Identity Provider.

-
On the Add Identity Provider window, select the IDP you want to configure.
-
Perform the IDP configuration steps:
Configure Microsoft Entra ID
-
Under Microsoft Entra ID, complete the following fields:
Field Description Name A unique name for the IDP. Active Turn on the Active toggle to activate the IDP. Authentication URL The endpoint URL is provided by the IDP support to handle authentication requests. This URL allows Thales Authenticator Lifecycle Manager to securely communicate with the IDP to validate user credentials and issue authentication tokens. Application/Client ID The client ID of the registered application or service that will use FIDO devices for user authentication. Client Secret A valid client secret generated for the registered application or service. Thales Authenticator Lifecycle Manager uses the client secret along with the Application/client ID to authenticate securely with the IDP. MS Graph API URL The URL (https://graph.microsoft.com/beta) used by Thales Authenticator Lifecycle Manager to connect with the Microsoft Graph API for operations such as user search, device assignment, and device revocation. 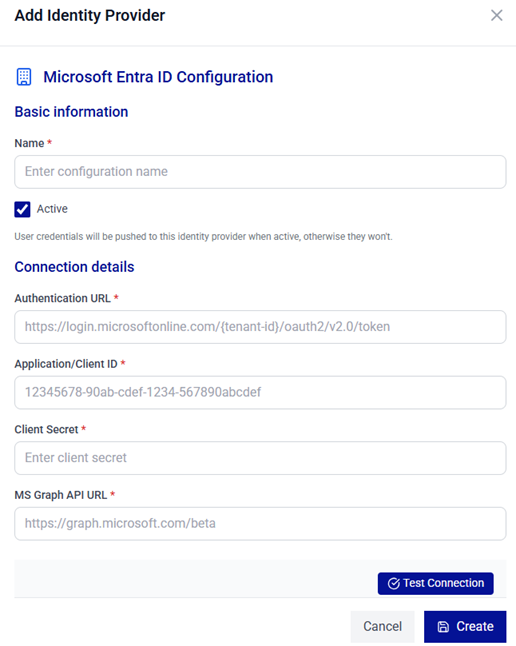
-
Click Test Connection.
Tip
Ensure that your Entra ID application registration is correctly configured, and that the client secret is valid and has not expired. Also, verify that both the authentication URL and the Microsoft Graph API URL are correct and aligned with your tenant and environment requirements.
-
(Optional) After a successful connection, scroll down to configure FIDO settings for the identity provider. This configuration allows administrators to control how FIDO authenticators are validated and to define which authenticators are permitted or blocked based on their Authenticator Attestation GUID (AAGUID).
Complete the following fields.
Field Description Enforce User Verification Specify whether user verification (such as a PIN or biometric) is required during FIDO authentication. Currently, Microsoft Entra ID only supports Required. Resident Key Indicates whether the FIDO credential is stored on the authenticator (resident credential). Currently, Microsoft Entra ID only supports true. Attestation Select the level of authenticator attestation required during registration. Currently, Microsoft Entra ID only supports True (Direct) and False (None). AAGUID List Select one of the two options (Allow and Block) to specify allowed or blocked AAGUIDs for the IDP. Allowed AAGUIDs / Blocked AAGUIDs Enter the AAGUIDs of authenticators to be allowed or blocked. Enter one AAGUID per line. The field name changes based on the option selected under AAGUID List. 
-
Click Create.
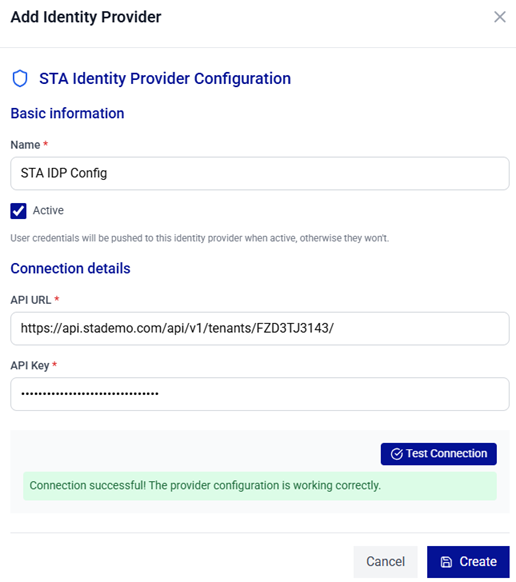
Configure STA Identity Provider
-
Under STA Identity Provider, complete the following fields:
Field Description Name A unique name for the IDP. Active Turn on the Active toggle to activate the IDP. API URL The endpoint URL required to handle authentication requests. This URL allows Thales Authenticator Lifecycle Manager to securely communicate with the IDP to validate user credentials and issue authentication tokens. API Key A valid STA API key provided by the identity provider (IDP) used to authenticate and authorize access to the SafeNet Trusted Access (STA) API. 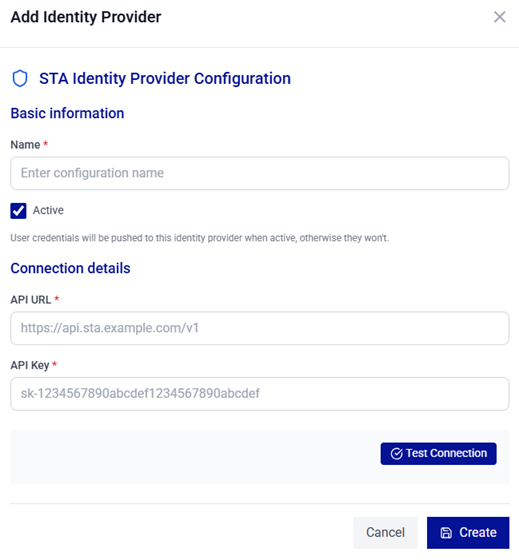
-
Click Test Connection.
-
After the connection is successful, click Create.
Configure PingOne
-
Under PingOne, complete the following fields:
Field Description Name A unique name for the IDP. Active Turn on the Active toggle to activate the IDP. Application/Client ID The client ID of the registered application or service that will use FIDO devices for user authentication. Client Secret A valid client secret generated for the registered application or service. Thales Authenticator Lifecycle Manager uses the client secret along with the Application/client ID to authenticate securely with the IDP. Auth Server Base URL The endpoint URL (https://auth.pingone.sg) handles the authentication requests. This URL allows Thales Authenticator Lifecycle Manager to securely communicate with the IDP to validate user credentials and issue authentication tokens. API Server Base URL The URL (https://api.pingone.sg/v1), used by Thales Authenticator Lifecycle Manager to connect with the Microsoft Graph API for operations such as user search, device assignment, and device revocation. Environment ID The unique identifier of a PingOne environment, used by Thales Authenticator Lifecycle Manager to connect to the correct PingOne tenant for operations such as authentication, user management, and API communication. 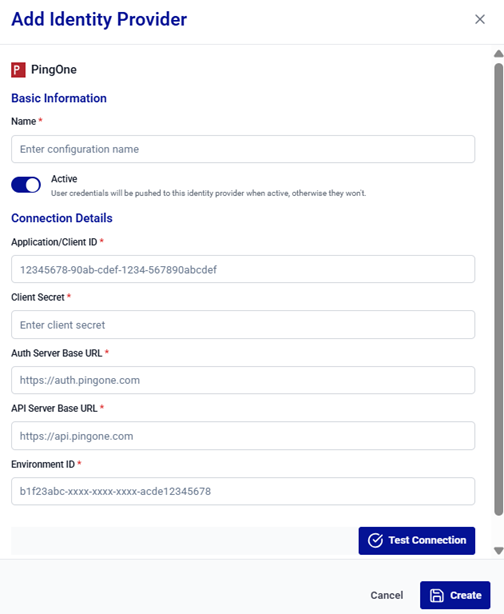
-
Click Test Connection.
-
After the connection is successful, click Create.
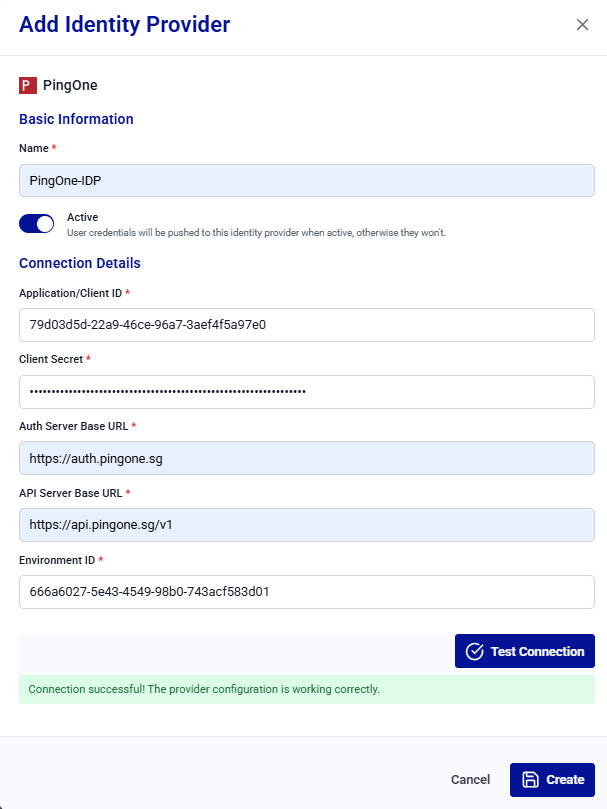
Tip
Ensure that your PingOne application registration is correctly configured, and that the client secret is valid and has not expired. Also, verify that both the Client ID (Application ID) and the Environment ID are correct and aligned with your tenant and environment requirements.
Configure Okta
-
Under Okta, complete the following fields:
Field Description Name A unique name for the IDP. Active Turn on the Active toggle to activate the IDP. Application/Client ID The client ID of the registered application or service that will use FIDO devices for user authentication. API URL The Okta API base URL (for example, https://integrator-5476601.okta.com/api/v1) for your tenant, used to perform operations such as user search, device assignment, and device revocation. Authorization URL The endpoint URL (for example, https://integrator-5476601.okta.com/oauth2/v1/authorize) used to handle authentication requests. This URL allows Thales Authenticator Lifecycle Manager to securely communicate with the IDP to validate user credentials and issue authentication tokens. Key ID The Key ID (KID) associated with the private key used to sign authentication requests. Private Key The private key used to enable secure communication and to sign authentication requests with Okta. 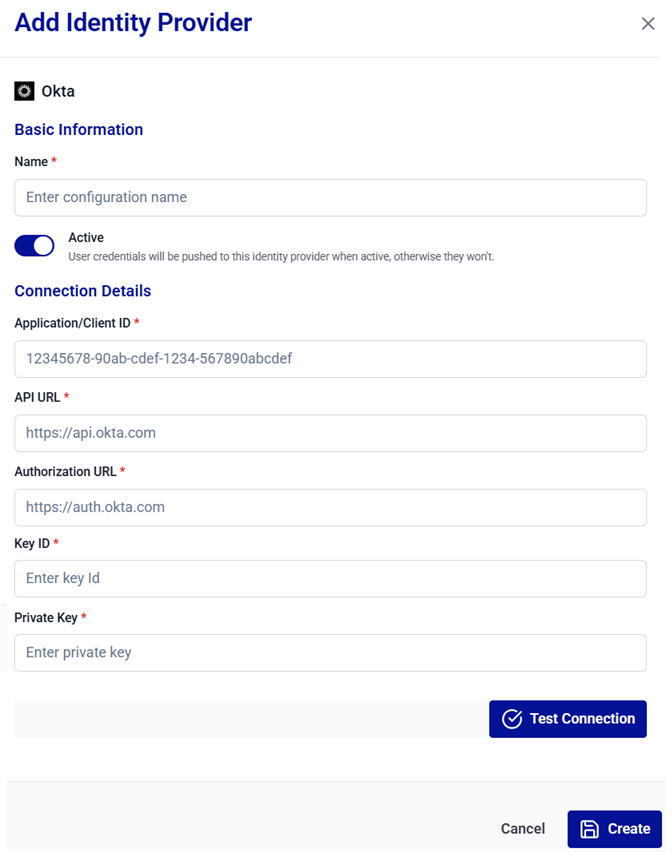
-
Click Test Connection.
-
After the connection is successful, click Create.
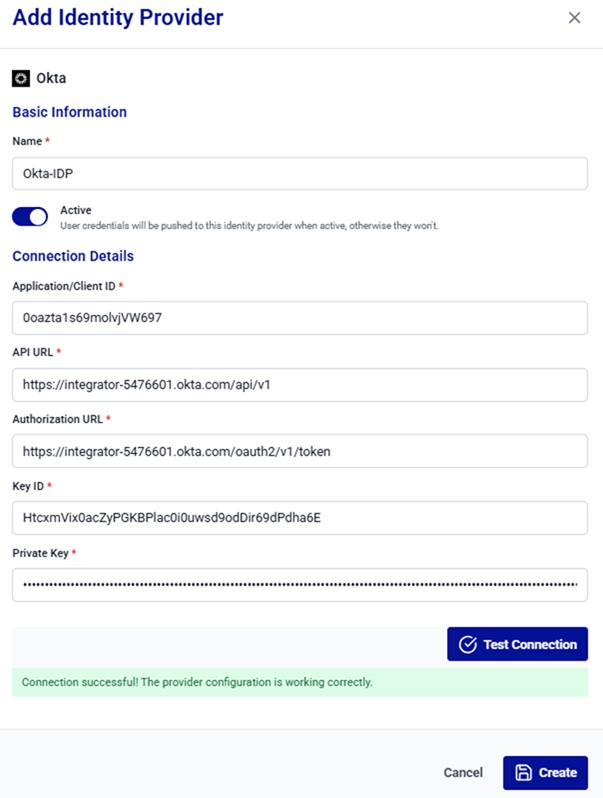
Tip
Ensure that your Okta application registration is correctly configured, and that the private key is valid and has not expired. Also, verify that the Client ID (Application ID) and the Key ID are correct and aligned with your tenant requirements.
-
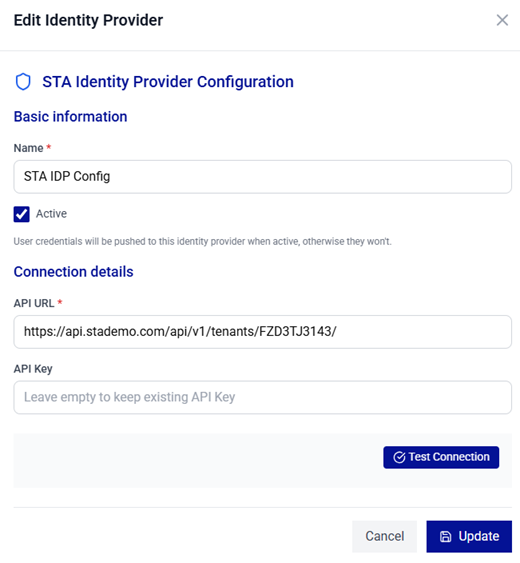
Edit an Identity Provider
-
On the Identity Provider Settings window, search for and locate the target identity provider name from the list.
-
In the Actions column, click the three-dots
 icon for the identity provider, and then select Edit.
icon for the identity provider, and then select Edit.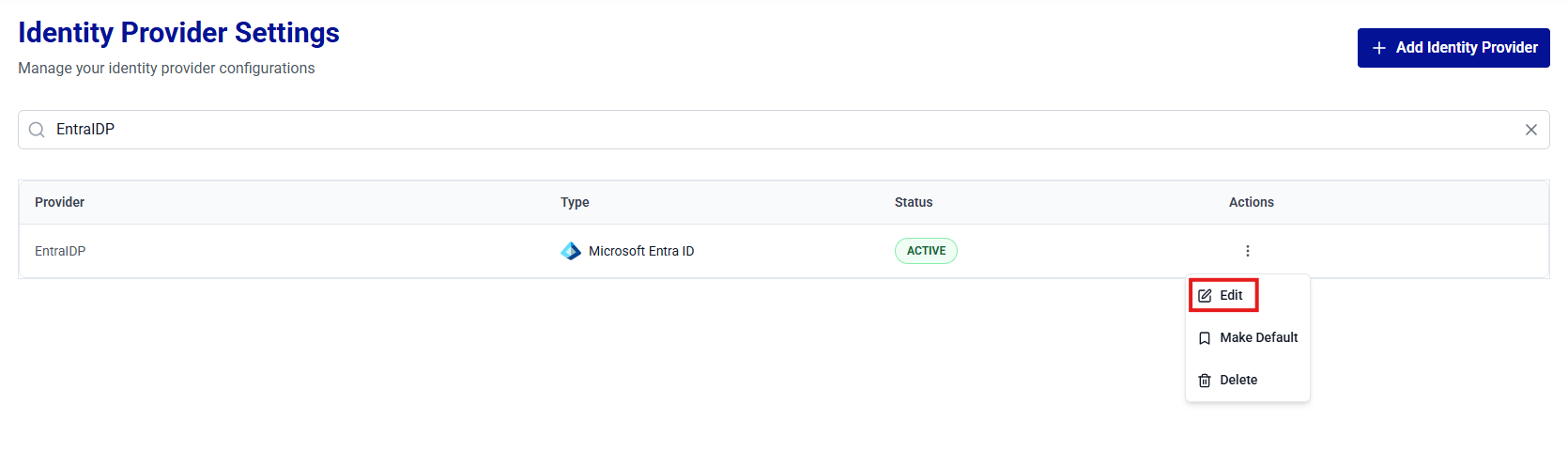
-
On the Edit Identity Provider window, update the IDP configuration as needed.
Note
For field descriptions, refer to step 3 of the Add Identity Providers section.
-
Click Test Connection to revalidate the configuration.
-
(Optional) Scroll down and update the FIDO Configuration, if applicable.
Caution
If the FIDO Configuration is updated for an existing Microsoft Entra ID IDP, the Client Secret must be entered. This value is required to save the changes.

-
Click Update to update the configuration.
Caution
When updating Client Secret for Entra ID or API Key for STA, coordinate with your identity provider support team to avoid authentication disruptions. Whenever possible, schedule these changes during a planned maintenance window.
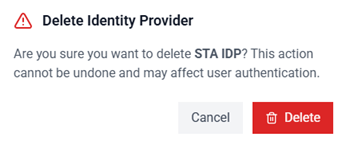
Delete an Identity Provider
-
On the Identity Provider Settings window, search for and locate the target identity provider name from the list.
-
In the Actions column, click the three-dots
 icon for the identity provider, and then select Delete.
icon for the identity provider, and then select Delete. 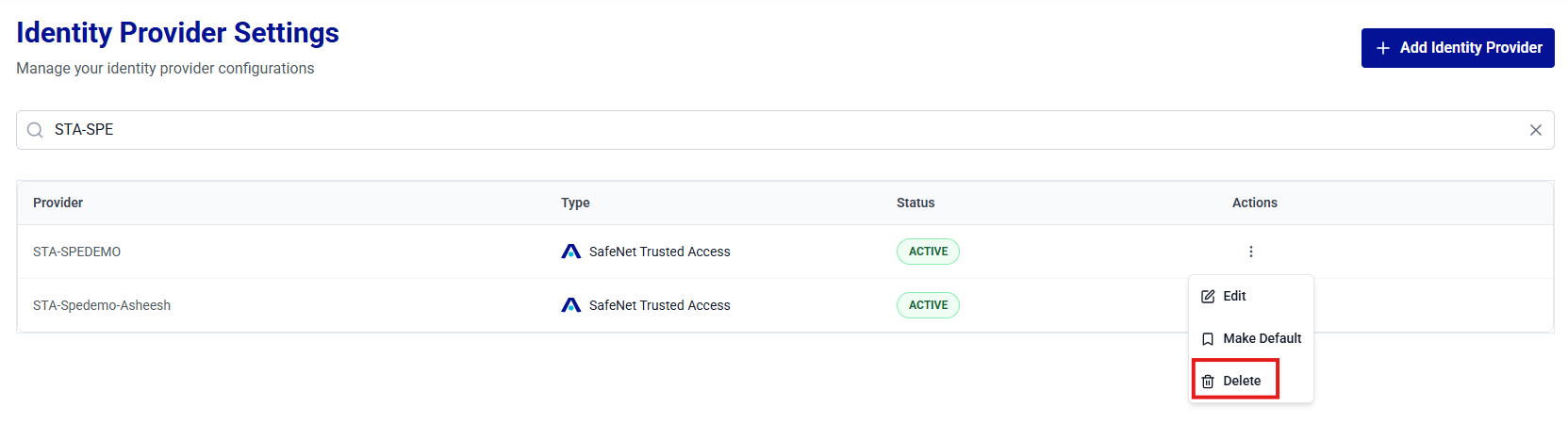
-
The Delete Identity Provider window is displayed. Click Delete to confirm the operation. The IDP configuration will be successfully removed.
Warning
Deleting an identity provider immediately disables user authentication via the IDP. Before proceeding, ensure that no critical workflows or dependencies rely on the IDP. After deletion, console users will no longer be able to revoke existing device assignments, search for users, or assign new devices.
Set a Default Identity Provider
Perform the following steps to set an identity provider as default:
-
On the Identity Provider Settings window, search for and locate the target identity provider name (for example, STA-IDP) from the list.
-
In the Actions column, click the three-dots
 icon for the identity provider, and then select Set as Default.
icon for the identity provider, and then select Set as Default.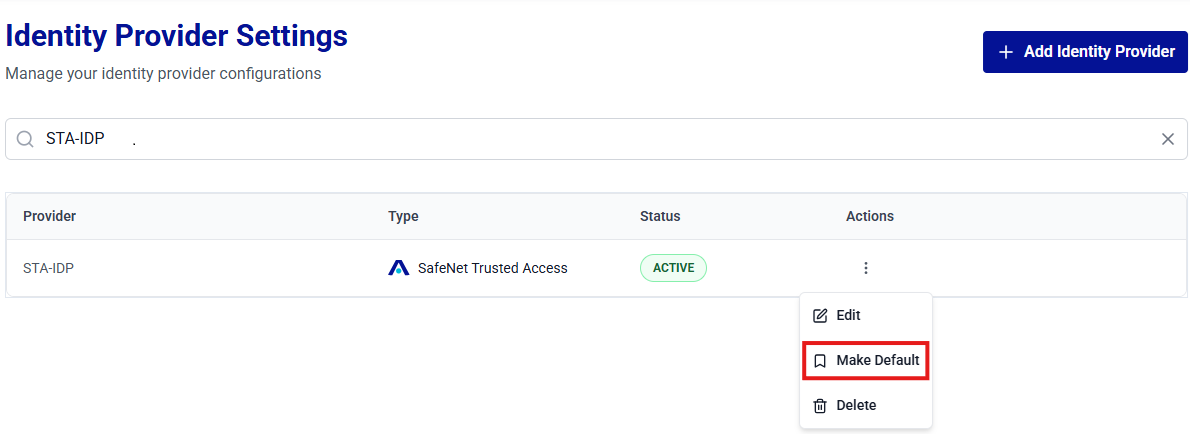
-
The Identity Provider (for example, STA-IDP) is set to default and the <IDP name> identity provider set as default. message is displayed.
The identity provider name is displayed with the DEFAULT indicator.
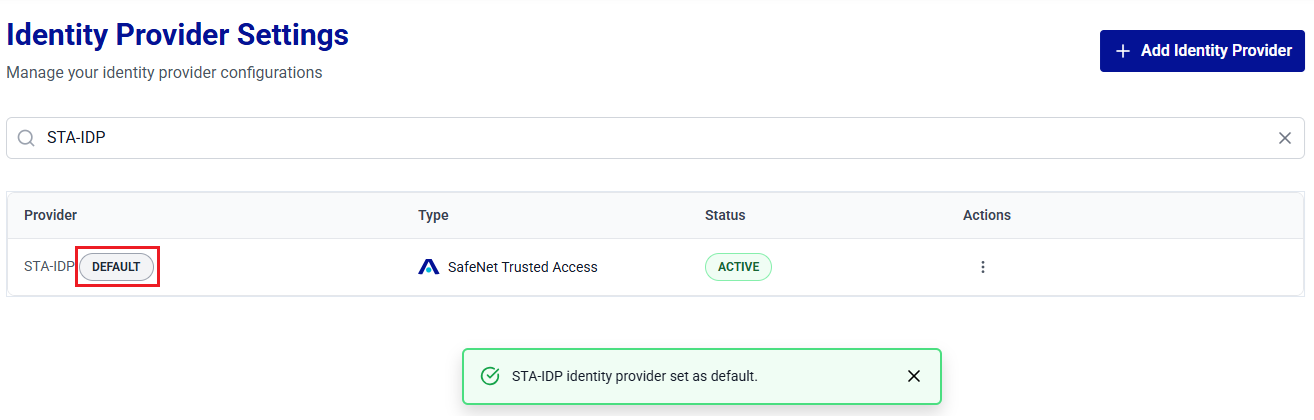
Note
Only one identity provider can be set as default at a time. Setting a new identity provider as default automatically clears the previous one.

