Interfaces
The primary channel to interact with DDC is through the CM's GUI, also called the console. The console allows you to perform the management operations, such as managing data stores and scans.
You can also interact with DDC by using the CLI. The CM includes a CLI tool, named ksctl, that can be downloaded and run locally to control a remote CM appliance. For more information, refer to CLI below.
In this guide we provide instructions to perform all management functions such as creating branch locations and data stores only through the CM console (GUI).
Accessing DDC in the Console
Use this procedure to get access to the DDC features in the GUI.
Open the CM URL in a browser. The log in page is displayed.
Enter Username and Password.
Click Log In. The GUI of the CM is displayed.
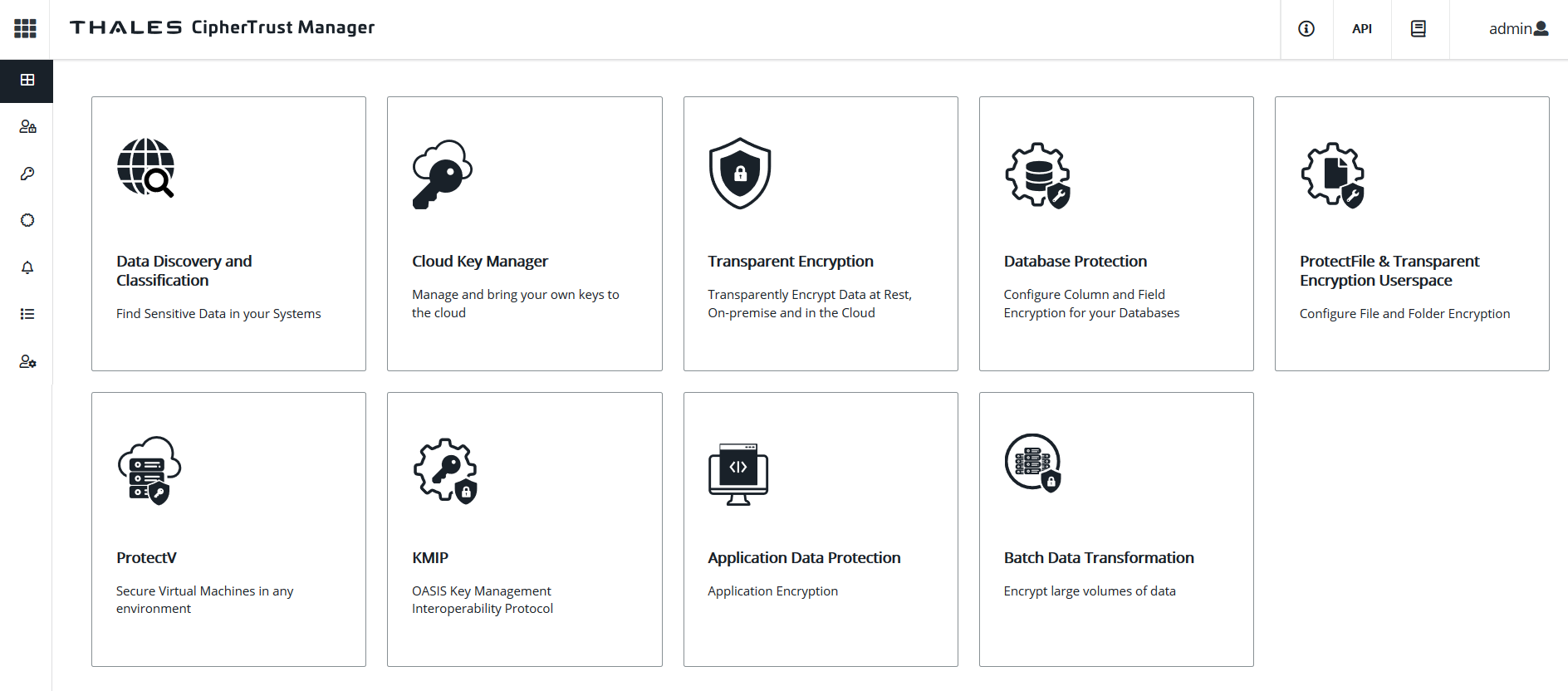
By default, the Applications page is displayed with links to various applications.
Click the Data Discovery link to open the Data Discovery application.
CLI
The CipherTrust Manager includes a CLI tool, named ksctl, that can be downloaded and run locally to control a remote CipherTrust Manager appliance. ksctl exclusively uses the REST API to communicate with CM, so anything that you can do with the tool, you can also do directly with the REST API. Conversely, ksctl exposes most of the functionality of the REST API. It can perform management functions, such as managing registration tokens and clients. ksctl is designed to be run from a remote system, not on CipherTrust Manager itself.
To use the CLI:
Open the CipherTrust Manager URL in a browser.
Click the API & CLI Documentation link. The API playground is displayed.
At the top left, click CLI Guide. The CLI documentation is displayed.
At the top right, click the CLI download button. This downloads the ksctl_images.zip file.
Unzip the ksctl_images.zip file.
Set up the ksctl-os file for your system.
Run ksctl ddc to run DDC specific commands.
Refer to the CipherTrust Manager documentation for details. For details on commands related to DDC, refer to the online documentation of ksctl ddc.

